How do I disable IP flood detection?
To Disable IP Flood Detection
Enter admin in the Username field.Enter motorola in the Password field.Click the Login button. The Status page appears.Click the Firewall link on top of the screen.Click the Web Filter link in the left-hand menu.In the Web Features section, check disable and click the Apply button.
What is HTTP flood attack?
HTTP flood is a type of Distributed Denial of Service (DDoS) attack in which the attacker exploits seemingly-legitimate HTTP GET or POST requests to attack a web server or application.
What is ICMP flood?
An Internet Control Message Protocol (ICMP) flood DDoS attack, also known as a Ping flood attack, is a common Denial-of-Service (DoS) attack in which an attacker attempts to overwhelm a targeted device with ICMP echo-requests (pings).
How does a ping flood work?
A ping flood is a denial-of-service attack in which the attacker attempts to overwhelm a targeted device with ICMP echo-request packets, causing the target to become inaccessible to normal traffic. When the attack traffic comes from multiple devices, the attack becomes a DDoS or distributed denial-of-service attack.
Should I disable IP flood detection?
Keep the IP Flood Detection off will generally improve your wireless speed on a home network. Disable IP Flood Detection by having it ticked off will help with your streaming speed for Apple and gaming speed like Call of Duty for Xbox Live.
What causes ARP flooding?
What causes ARP flooding? Address Resolution Protocol (ARP) flooding, also known as ARP spoofing, happens when an attacker has sent forged ARP messages. Once the attacker’s MAC address is connected to an authentic IP address, all the intended data for the authentic user will be received by the attacker as well.
How do you detect a SYN flood attack?
What Are the Signs of a SYN Flood DDoS Attack?
The three-way handshake is initiated when the client system sends a SYN message to the server.The server then receives the message and responds with a SYN-ACK message back to the client.Finally, the client confirms the connection with a final ACK message.
How many requests is a DDoS?
JavaScript-Based DDoS Peaks at 275,000 Requests Per Second | Threatpost.
What is fast flood attack?
An HTTP flood attack is a type of volumetric distributed denial-of-service (DDoS) attack designed to overwhelm a targeted server with HTTP requests. Once the target has been saturated with requests and is unable to respond to normal traffic, denial-of-service will occur for additional requests from actual users.
Is ping flooding illegal?
It is illegal to send a ping packet of size greater than 65,535, but a packet of such size can be sent if it is fragmented. When a receiving computer reassembles the packet, a buffer overflow occurs, which often causes computer to crash.
What is the ping of death command?
Ping of Death (a.k.a. PoD) is a type of Denial of Service (DoS) attack in which an attacker attempts to crash, destabilize, or freeze the targeted computer or service by sending malformed or oversized packets using a simple ping command.
What is ICMP and UDP flood?
Description. UDP and ICMP Flood attacks are a type of denial-of-service (DoS) attack. They are initiated by sending a large number of UDP or ICMP packets to a remote host. The appliance monitors UDP or ICMP traffic to a specified destination or to any destination.
Can you DDoS a router?
Yes, by overwhelming the network or local host with repeated meanless request for network resources. You will need other computers, devices or IoTs to perform the cyber attack. To DDoS you need hundreds to thousands of systems to simultaneously attack your router.
How do I stop ICMP?
To disable more than one type of ICMP message, enter the no ip icmp unreachable command for each messages type. The host parameter disables ICMP Host Unreachable messages. The protocol parameter disables ICMP Protocol Unreachable messages.
How do I ping an IP address?
How to run a ping network test
Type “cmd” to bring up the Command Prompt.Open the Command Prompt.Type “ping” in the black box and hit the space bar.Type the IP address you’d like to ping (e.g., 192. XXX. X.X).Review the ping results displayed.
What is flood limit?
The maximum flood insurance coverage amount is $250,000 for the structure of the home and $100,000 for the contents of the home.
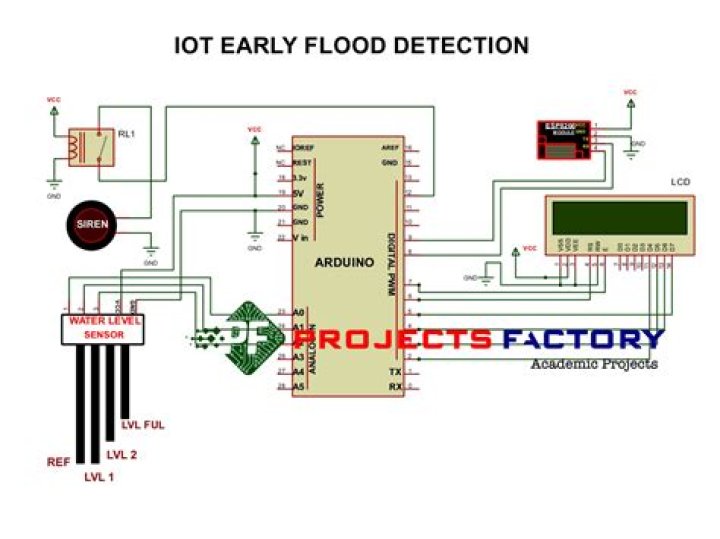
What is anti flood IP?
An IP Flood is a form of malicious attack that may be perpetrated against a single device or an entire network. This is a DoS attack (Denial of Service) that aims to disrupt the normal function of a device and prohibit it from sending requests or processing information.
What does disable port scan do?
The Disable Port Scan and DoS Protection feature can be enabled or disabled in the NETGEAR router GUI. This causes a Denial of Service (DoS) and results in slow access to the Internet, since the amount of traffic attempting to ping your IP address overloads the router.
Related Archive
harry potter wizards unite apple, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter uniform shop, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter wand name list, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
