session fixation vs session hijacking, check these out | What is session fixation?
In the session hijacking attack, the attacker attempts to steal the ID of a victim’s session after the user logs in. In the session fixation attack, the attacker already has access to a valid session and tries to force the victim to use that particular session for his or her own purposes.
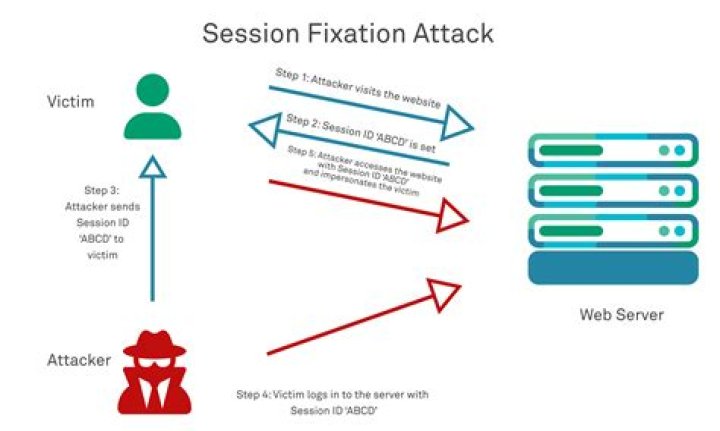
What is session fixation?
Session Fixation is an attack that permits an attacker to hijack a valid user session. The attack explores a limitation in the way the web application manages the session ID, more specifically the vulnerable web application.
What is session hijacking?
Session hijacking, also known as TCP session hijacking, is a method of taking over a web user session by surreptitiously obtaining the session ID and masquerading as the authorized user.
What is the difference between session hijacking and IP spoofing?
A spoofing attack (see Chapter 4, “Spoofing”) is different from a hijack in that an attacker is not actively taking another user offline to perform the attack. Instead, he pretends to be another user or machine to gain access.
What is session fixation protection?
Session fixation is a web-based attack technique where an attacker tricks the user into opening a URL with a predefined session identifier. Session fixation attacks can allow the attacker to take over a victim’s session to steal confidential data, transfer funds, or completely take over a user account.
What is the impact of session fixation?
Impact. A successful session fixation attack gives the attacker access to the victim’s account. This could mean access to higher level privileges or the ability to look at sensitive data.
How session fixation helps attackers to hijack a valid user session explain?
Session fixation is a web attack technique. The attacker tricks the user into using a specific session ID. After the user logs in to the web application using the provided session ID, the attacker uses this valid session ID to gain access to the user’s account.
What is an example of session hijacking?
What is session hijacking? A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or shopping at an online store. Session hijackers usually target browser or web application sessions.
What are the types of session hijacking?
The two main types of session hijacking are Application Layer Hijacking and Transport Layer Hijacking. Each type includes numerous attack types that enable a hacker to hijack a user’s session.
What is session hijacking and its various types?
There are two types of session hijacking depending on how they are done. If the attacker directly gets involved with the target, it is called active hijacking, and if an attacker just passively monitors the traffic, it is passive hijacking.
Is session hijacking a vulnerability?
The threat of session hijacking exists due to stateless protocol. These protocols have limitations, which is why they are vulnerable to attacks.
What defense works best against session fixation?
Creating a new session identifier upon login is the most critical defense against session fixation attacks. Instead of authenticating the user’s existing (pre-authenticated) session identifier, the application should grant the user a new, authenticated session identifier.
What is session fixation in Java?
Session fixation, by most definitions, is a subclass of session hijacking. The most common basic flow is: Step 1. Attacker gets a valid session ID from an application. Step 2.
What is clickjacking example?
Clickjacking is an attack that tricks a user into clicking a webpage element which is invisible or disguised as another element. This can cause users to unwittingly download malware, visit malicious web pages, provide credentials or sensitive information, transfer money, or purchase products online.
What is an example of a session related vulnerability?
Session Variable Example
If a user called Alice logged in, she would be greeted with “Hello Alice”. If Bob was logged in at the same time and opened the same page, he would see “Hello Bob” instead. The session variable is available across different files and isn’t restricted to file it is declared in.
What is RST hijacking?
RST hijacking involves injecting an authentic-looking reset (RST) packet using spoofed source address and predicting the acknowledgment number. The victim believes that the source actually sent the reset packet and resets the connection.
Which are the section related vulnerabilities?
The Top 10 security vulnerabilities as per OWASP Top 10 are:
SQL Injection.Cross Site Scripting.Broken Authentication and Session Management.Insecure Direct Object References.Cross Site Request Forgery.Security Misconfiguration.Insecure Cryptographic Storage.Failure to restrict URL Access.
Related Archive
harry potter wizards unite wand guide, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter villain test, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
harry potter uk edition books, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023