What characteristic of a network enables it to quickly grow to support new users and applications wi
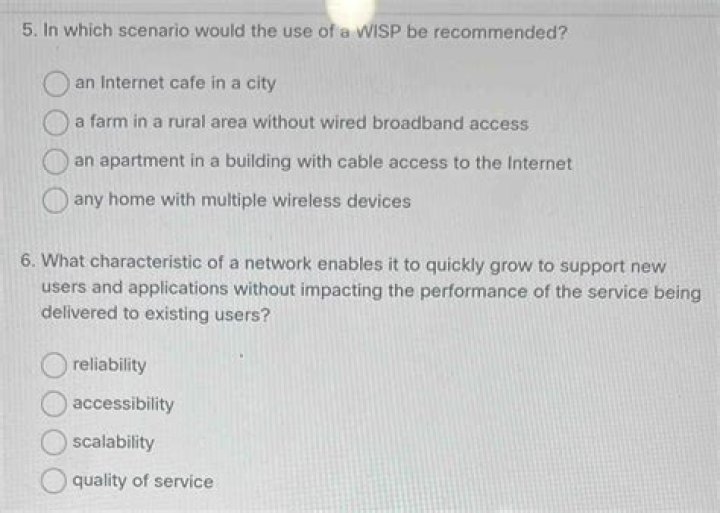
What characteristic of a network enables it to quickly grow to support new users and applications without impacting the performance of the service Bei?
Networks must be able to quickly grow to support new users and services, without impacting existing users and services. This ability to grow is known as scalability.
What is a network feature that would allow an employee to gain secure remote access to a company network?
What network feature would allow an employee to gain secure remote access to a company network? Explanation: Virtual private networks (VPN) are used to provide secure access to remote workers.
Which three devices are considered end devices in a network?
Some examples of end devices are:
computers (workstations, laptops, file servers, and web servers)nsetwork printers.VoIP phones.TelePresence endpoints.security cameras.
What are the two functions of end devices on a network?
They direct data over alternate paths in the event of link failures. They filter the flow of data to enhance security. They are the interface between humans and the communication network. They provide the channel over which the network message travels.
What is a characteristic of a peer to peer application?
Characteristics of Peer to Peer Computing
Peer to peer networks are usually formed by groups of a dozen or less computers. These computers all store their data using individual security but also share data with all the other nodes. The nodes in peer to peer networks both use resources and provide resources.
Which of the following are business class Internet connection technologies normally supplied by a service provider choose two?
Leased line and Metro Ethernet are considered business-class Internet connection technologies.
What are some methods companies might employ to secure their network while enabling employees to use personal devices especially while working remotely?
6 Ways to Keep Employer Data Secure When Working Remotely
Establish a Cybersecurity Policy. Ensure all Internet Connections Are Secure. Keep Passwords Strong and Varied — and Use a Password Manager. Rely on Two-Factor Authentication. Use Encryption Software. Don’t Forget Firewalls, Antivirus Software and Anti-Malware.
Which criterion can be used to select the appropriate type of network media for a network?
The criteria for choosing network media are: the distance the media can successfully carry a signal. the environment in which the media is to be installed. the amount of data and the speed at which it must be transmitted.
How are you going to help the staff to work from home and access the network inside the company in a secure way?
Top tips to safeguard your network when employees are working from home
Provide VPN access to your employees. Ensure complete security of your VPN. Use MAC binding. Implement multi-factor authentication. Discourage the use of third-party remote access platform.
What allows digital devices to interconnect and transmit data?
A network is what allows digital devices to interconnect and transmit data. A computer network or data network is a telecommunications network which allows computers to exchange data .
Which connection physically connects the end device to the network?
Network Interface Card – A NIC, or LAN adapter, provides the physical connection to the network at the PC or other end device.
What is a network switch and what does it do?
A network switch, otherwise known as a switching hub, a bridging hub or a MAC bridge, is a small piece of hardware that manages the communications of multiple connected devices in a single, wired local area network (LAN).
What happens when two devices on the same subnet are communicating?
What happens when two devices on the same subnet are communicating? The host portion of the IP addresses will be different. When two devices are on the same local network, the network portion of their IP addresses will be the same and the host portion of their IP addresses will be different.
What is connecting devices in networking?
Advertisements. Hardware devices that are used to connect computers, printers, fax machines and other electronic devices to a network are called network devices. These devices transfer data in a fast, secure and correct way over same or different networks.
Which two actions improve security on a wireless network?
What can you do to minimize the risks to your wireless network?
Change default passwords. Restrict access. Encrypt the data on your network. Protect your Service Set Identifier (SSID). Install a firewall. Maintain antivirus software. Use file sharing with caution. Keep your access point software patched and up to date.
How do peer-to-peer networks work?
In a peer-to-peer network, computers on the network are equal, with each workstation providing access to resources and data. This is a simple type of network where computers are able to communicate with one another and share what is on or attached to their computer with other users.
What is peer-to-peer network advantages?
Key advantages of using a P2P network
Easy file sharing: An advanced P2P network can share files quickly over large distances. Files can be accessed anytime. Reduced costs: There is no need to invest in a separate computer for a server when setting up a P2P network.
What is the importance of peer-to-peer network and client-server network?
Client/server networks are more expensive. Most home networks have only five or fewer PCs, which is well within the capabilities of a peer-to-peer network. Most important, in a peer-to-peer network you can share files, share printers, create passwords, and do most of the things you do with a client/server network.
Related Archive
harry potter wizards unite apple, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter uniform shop, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter wand name list, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
