What is the best protection method for sharing personally identifiable information?
What is the best protection method for sharing Personally Identifiable Information (PII)? Digitally sign and encrypt the email.
What is the best way to protect your CAC?
To protect the information on your CAC, you should never tell anyone your PIN or write it down where it can be easily found. Your PIN should be kept secure at all times, just like your Social Security Number.
Which of the following is the best example of protected health information?
Health information such as diagnoses, treatment information, medical test results, and prescription information are considered protected health information under HIPAA, as are national identification numbers and demographic information such as birth dates, gender, ethnicity, and contact and emergency contact
What must you ensure before transmitting Personally Identifiable Information (PII) or Protected Health Information (PHI) via e-mail? Transmissions must be between Government e-mail accounts and must be encrypted and digitally signed when possible. Encrypt the e-mail and use your Government e-mail account.
Under what circumstances is it acceptable to check personal?
Under what circumstances is it acceptable to check personal email on Government-furnished equipment (GFE)? If your organization allows it. When checking in at the airline counter for a business trip Decline so that you maintain physical contact of your Government-issued laptop.
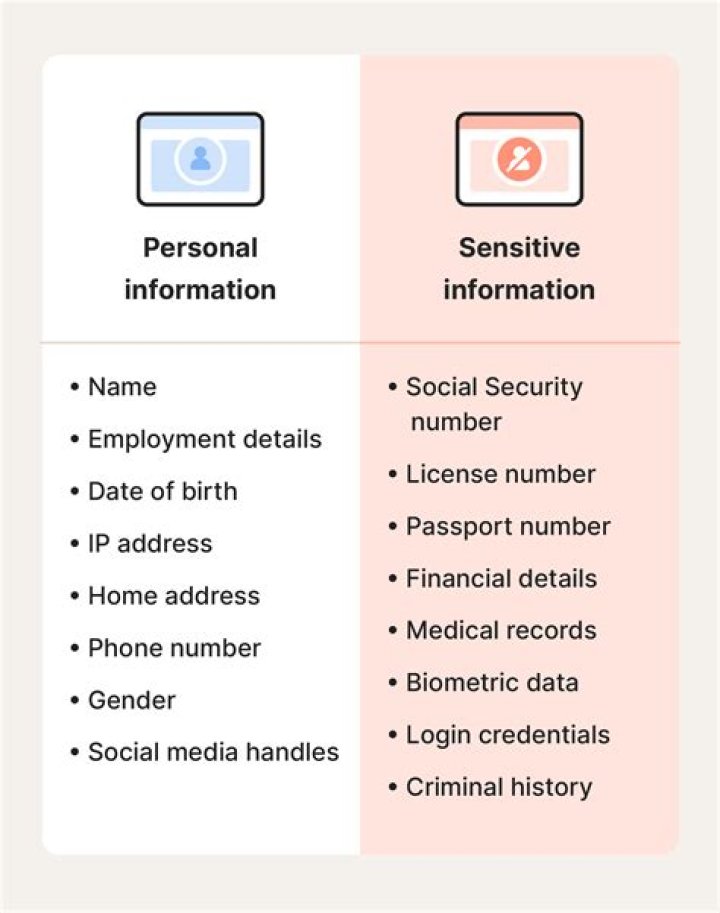
Personally identifiable information, or PII, is any data that could potentially be used to identify a particular person. Examples include a full name, Social Security number, driver’s license number, bank account number, passport number, and email address.
What does personally identifiable information include?
The United States Government Accountability Office defines Personal Identifiable Information (PII) as “… information that can be used to locate or identify an individual, such as names, aliases, Social Security numbers, biometric records, and other personal information that is linked or linkable to an individual.
What kind of personally identifiable health information is protected by Hipaa Privacy Rule?
Protected Health Information.
The Privacy Rule protects all “individually identifiable health information” held or transmitted by a covered entity or its business associate, in any form or media, whether electronic, paper, or oral. The Privacy Rule calls this information “protected health information (PHI).”
What is the best example of Protected Health information (PHI)? Your health insurance explanation of benefits (EOB).
Which of the following is the best definition of electronic protected health information ePHI )?
Electronic protected health information or ePHI is defined in HIPAA regulation as any protected health information (PHI) that is created, stored, transmitted, or received in any electronic format or media. HIPAA regulation states that ePHI includes any of 18 distinct demographics that can be used to identify a patient.
What is a good practice to protect classified information?
Which is good practice to protect classified information? Ensure proper labeling by appropriately marking all classified material. Which classification level is given to information that could reasonably be expected to cause serious damage to national security?
What should you do if a reporter asks you about potentially classified information on the Web 2021?
(Spillage) What should you do if a reporter asks you about potentially classified information on the web? Refer the reporter to your organization’s public affairs office.
What is the best response if you find classified government data on the internet? Note any identifying information, such as the website’s URL, and report the situation to your security POC.
Under which circumstances is it permitted to share an unclassified?
Is it permitted to share an unclassified draft document with a non-DoD professional discussion group? As long as the document is cleared for public release, you may share it outside of DoD. Within a secure area, you see an individual you do not know.
What is a good practice to protect data on your home wireless systems?
What is a good practice to protect data on your home wireless systems? Ensure that the wireless security features are properly configured. You just studied 2 terms!
When Should documents be marked within a SCIF?
~All documents should be appropriately marked, regardless of format, sensitivity, or classification. Unclassified documents do not need to be marked as a SCIF. Only paper documents that are in open storage need to be marked.
Which of the following is a best practice for securing your home computer? Use antivirus software and keep it up to date.
What are some actions you can take to protect your identity cyber awareness?
How to protect yourself against cybercrime
Use a full-service internet security suite. Use strong passwords. Keep your software updated. Manage your social media settings. Strengthen your home network. Talk to your children about the internet. Keep up to date on major security breaches.
Related Archive
harry potter wizards unite apple, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter uniform shop, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter wand name list, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
