What type of radio frequency transmissions are used by Bluetooth devices?
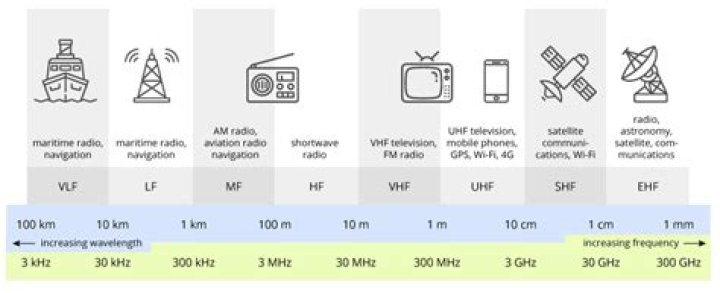
Instead of transmitting over one frequency within the 2.4 GHz band, Bluetooth radios use a fast frequency-hopping spread spectrum (FHSS) technique, allowing only synchronized receivers to access the transmitted data.
What direction do access point antennas radiate their signals and where should they be located?
Access point antennas should Radiate in All Directions and should be Centrally located.
Which EAP protocol creates an encrypted channel between the client authentication server and the client?
-Protected Extensible Authentication Protocol (EAP-PEAP. A widely used protocol for securely transporting authentication data across a network (tunneled).) is a protocol that creates an encrypted (and more secure) channel before the password-based authentication occurs. PEAP.
What device acts like a wireless base station in a network acting as a bridge?
A wireless access point, also known as wireless AP or WAP, stands for a networking hardware appliance that adds Wi-Fi capability to the existing wired network by bridging traffic from wireless stations into wired LAN. The wireless AP can act as a stand-alone device or can be a component of a router.
What is the maximum range of most Bluetooth devices?
The range of the Bluetooth® connection is approximately 30 feet (10 meters). However, maximum communication range will vary depending on obstacles (person, metal, wall, etc.) or electromagnetic environment. NOTE: Not all audio devices are supplied with Bluetooth capability.
What is the maximum range of most Bluetooth five devices?
With Bluetooth 5.0, the wireless technology is capable of 4x the range, going from 200 feet (60 meters) to 800 feet (240 meters).
Why it is important to be able to control the power level at which the WLAN transmits?
Explain why it is important to be able to control the power level at which the WLAN transmits. It is important to be able to control the power level because if a signal is strong enough that it leaves the premises of a building, an attacker would be able to connect into the network.
What security concept states a user should only be given the minimum set of permissions required to perform necessary tasks?
The principle of least privilege (PoLP) refers to an information security concept in which a user is given the minimum levels of access – or permissions – needed to perform his/her job functions.
What is the name for the common Omni directional antennas found on wireless access points?
What is the name for the common omni-directional antennas found on wire- less access points? B. Standard omni-directional antennas are called dipole antennas. Ralph has installed a wireless network in his house, placing the wireless access point in the kitchen, a centralized location.
What is the maximum transmission power for IEEE WLANs?
For IEEE WLANs, the maximum transmit power is 200 milliwatts (mW).
Which encryption protocol is used in the WPA2 standard?
WPA2 is an updated version of WPA that uses AES encryption and long passwords to create a secured network.
What type of dedicated cryptographic processor that provides protection for cryptographic keys?
A hardware security module (HSM) is a dedicated crypto processor that is specifically designed for the protection of the crypto key lifecycle.
What features are supplied by WPA2?
Like its predecessor, WPA2 also offers enterprise and personal modes. WPA2 replaces RC4 and TKIP with two stronger encryption and authentication mechanisms: Advanced Encryption Standard (AES) and Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP), respectively.
Why is a rogue AP a security vulnerability?
Why is a rogue AP a security vulnerability? It allows an attacker to bypass network security configurations.
How does the WPA Temporal Key Integrity Protocol encryption technology operate?
While WEP provides each authorized system with the same key, WPA uses the temporal key integrity protocol (TKIP), which dynamically changes the key that the systems use. This prevents intruders from creating their own encryption key to match the one used by the secure network.
What determines Bluetooth range?
Bluetooth® technology uses the 2.4 GHz ISM spectrum band (2400 to 2483.5 MHz), which enables a good balance between range and throughput. In addition, the 2.4 GHz band is available worldwide, making it a true standard for low-power wireless connectivity.
What affects Bluetooth range?
Ranges can be drastically reduced by obstacles between the two devices, such as walls, which attenuate the signals. Thus, the range is affected by transmitting power, receiver sensitivity and obstacles near the device.
What is the typical range for the use of Bluetooth quizlet?
A wireless standard that enables devices to transmit data at up to 721.2 Kbps over a typical maximum distance of 33 feet. Bluetooth can transmit data farther, but devices that can use this capability are rare.
Related Archive
harry potter wizards unite wand guide, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter villain test, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
harry potter uk edition books, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023