Which of the following is secure programming guidelines?
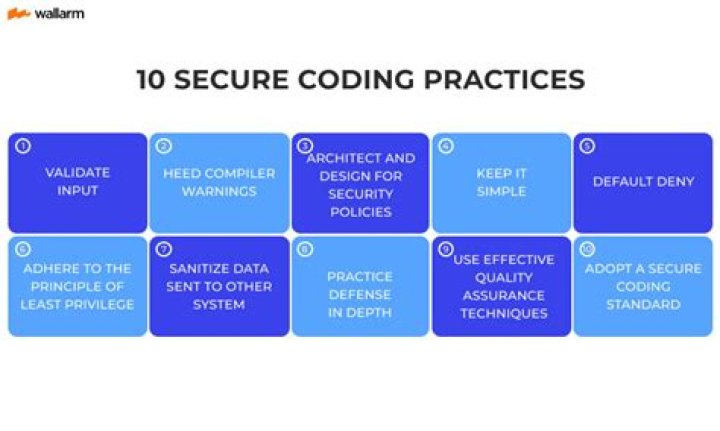
8 Secure Coding Best Practices
Security by Design.Password Management.Access Control.Error Handling and Logging.System Configuration.Threat Modeling.Cryptographic Practices.Input Validation and Output Encoding.
What are secure programming policies?
Secure coding standards are rules and guidelines used to prevent security vulnerabilities. Used effectively, these security standards prevent, detect, and eliminate errors that could compromise software security.
Which of the following is a secure coding practice?
The following minimum set of secure coding practices should be implemented when developing and deploying covered applications: Formalize and document the software development life cycle (SDLC) processes to incorporate a major component of a development process: Requirements. Architecture and Design.
What are secure coding concepts?
Secure coding is a set of practices that applies security considerations to how software will be coded and encrypted to best defend against cyber attack or vulnerabilities. Secure coding standards introduce safeguards that reduce or eliminate the risk of leaving security vulnerabilities in code.
Which of the following is a security advantage of managed code?
What are the advantages of using Managed Code? It improves the security of the application like when you use runtime environment, it automatically checks the memory buffers to guard against buffer overflow. It implement the garbage collection automatically. It also provides runtime type checking/dynamic type checking.
What are security standards?
Security standards can be defined as a set of rules for products or processes that provides consistency, accountability, and efficiency. The use of written standards can be based on compliance and best practices. This enables organizations to make objective decisions concerning the implementation of security devices.
Which is the most secure programming language?
C is the indisputable winner of the bunch, with most vulnerabilities year after year, C also has a relatively low rate of low severity vulnerabilities reaching 7% in 2018.
What is a secure coding checklist?
The Secure Coding Practices Quick Reference Guide is a technology agnostic set of general software security coding practices, in a comprehensive checklist format, that can be integrated into the development lifecycle. At only 17 pages long, it is easy to read and digest.
Which is not secure coding practice?
2. Improper Exception Handling. I recently wrote about this insecure practice when looking at common pitfalls in python exception handling with regards to overly generic exception handling – but there are many other insecure ways to implement error handling in many different languages.
What is secure coding training?
The Secure Coding Dojo is a training platform which can be customized to integrate with custom vulnerable websites and other CTF challenges. The project was initially developed at Trend Micro and was donated to OWASP in 2021.
What is secure programming with C?
The purpose of C Secure is to specify secure coding rules that can be automatically enforced. These can be used to detect security flaws in C programming. To be considered a security flaw, a software bug must be triggerable by the actions of a malicious user or attacker.
What is secure programs in information security?
Definition. Secure programming is a way of writing codes in a software so that it is protected from all kinds of vulnerabilities, attacks or anything that can cause harm to the software or the system using it. Because it deals with securing the code, secure programming is also known as secure coding.
Why is secure programming important?
Secure coding practices find and remove vulnerabilities that could be exploited by cyber attackers from ending up in the finished code. It’s important to ensure any software developed has checks and system in place that helps strengthen the software and get rid of any security issues like vulnerabilities.
Which of the following is the secure method of authentication?
Nowadays, the usage of biometric devices such as hand scanners and retinal scanners is becoming more common in the business environment. It is the most secure method of authentication.
Which type of authentication is most secure?
Experts believe that U2F/WebAuthn Security Keys are the most secure method of authentication. Security keys that support biometrics combine the Possession Factor (what you have) with the Inherence Factor (who you are) to create a very secure method of verifying user identities.
Which of the following is one of the cyber security goals?
Protect the confidentiality of data. Preserve the integrity of data. Promote the availability of data for authorized users.
Related Archive
harry potter wizards unite wand guide, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023

harry potter villain test, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023
harry potter uk edition books, latest free online harry potter movies, best HD videos you should watch in 2022 – 2023